“My whole life I wanted to be a great inventor. Just like my hero.” – Flint Lockwood, “Cloudy with a Chance of Meatballs 2,” Columbia Pictures, 2013
Before the always-on, always-connected online world, folks would spend summer afternoons lying by a creek staring at the clouds and identifying them – planes, dragons, bunnies, snakes, hawks, and mermaids, anything they could imagine.
It was all in the mind of the beholder.
According to last year’s IBM survey, three-quarters (72 percent) of C-level executives worldwide said technology was changing the way they viewed their world on the ground and in the sky.
Cloud-based solutions will have a greater impact on their firm than any other technology or market factor. Here’s what people see the cloud providing:
– The CEO — a way to lower his IT spending
– Marketing — a way to reach more prospects
– Sales — a way to close more business, sell more stuff
– Service/support – a way to serve customers
– Film/game developers — a way to tap into viewers/users
– News outlets — a way to get breaking news out fast, attract more viewers/readers
– Families, friends — a way to keep in touch with each other
– Hackers, crooks — an opportunity to steal just about anything
There’s no “one-size-fits all” cloud for business today.
It’s what you want/need at that point in time. And it’s easily, economically changed.
Office Load
For businesses, the cloud is a place for collaboration, innovation, value creation, lower costs, greater returns, organizational flexibility, resource pooling and measured services as well as speed to market and response to company and competitive needs.
Whether it’s the private, public or hybrid cloud; companies are spending a lot of time and money integrating their legacy systems with cloud services.
The worldwide study by IBM late last year also found that 63 percent of the C-level executives believed that cloud computing services were vital to their activities
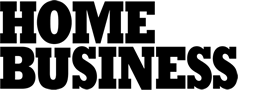
Analysts estimate that more than four-fifths (86 percent) of workloads will be processed by cloud data centers and 14 percent by traditional data centers over the next three years.
Cloud Work – To keep up with the rapidly changing global business environment, every company – large and small – is looking to implement cloud services and capabilities to economically remain flexible and competitive. Adding cloud-based computing, storage and services it is not without its risks.
Businesses basically have four options to choose from for their services in the U.S. – AWS (Amazon Web Services), Microsoft, Google and IBM. There are an equal number of strong service providers in other portions of the globe
There are also a ton of secondary cloud service providers as well as market/application-specific services that use the big four in the background.
The most important selection criteria for firms are:
– 71 percent – cost
– 58 percent – reliability
– 41 percent – data security controls
– 32 percent – customer support
In addition, firms weigh their decisions based on cloud storage, productivity, and computing providers they’re investing in. The soft question is which do you feel most comfortable with?
To entice you, they’re offering a dizzying array of services.
Serving Up – To ramp up and tune down various aspects of their business economically, most firms are taking advantage of the growing number of suppliers who have switched from selling their products to offering the solution as a service. And the service sales are growing rapidly.
The range of tailored services and the ease/speed of implementing them in work groups have created a massive shadow IT market that includes online expense-management tools, web-based email, word processing, social networks and entertainment. The attraction is launching business- specific processes quickly without waiting for IT to develop the application for the team.
Some are so easy to initiate that anyone with a credit card can start running work-specific jobs in minutes.
Cisco reported that CIOs estimate they use an average of 91 tailored services; others say the average is close to 1,120.
The actual figure is probably somewhere in between.
For example, CityMD, an urgent medical care service in New York, was formally supporting 15-20 but found they were actually using 520 cloud services.
The only thing researchers agree on is that the shift is taking place … whether management realizes it and likes it or not.
Workload Growth – Businesses and individuals are creating a tremendous volume of content, data and information that is moved around the globe. Most of the content being sent over the Internet is social media and entertainment.
In many instances, marketing leads the shift.
According to EverString, more than a third of businesses (38 percent) have a basic set of cloud services with a quarter of the firms using online CRM and exploring other marketing automation services.
Their goal is to quickly take advantage of technology to orchestrate and manage more timely, more effective customer interactions.
Personal Load
Add-Ons – Device manufacturers always promote their killer products (those that are going to eliminate earlier devices), but few really die. Most of the time, consumers simply add another device to their arsenal of tools they use in their business and personal lives.
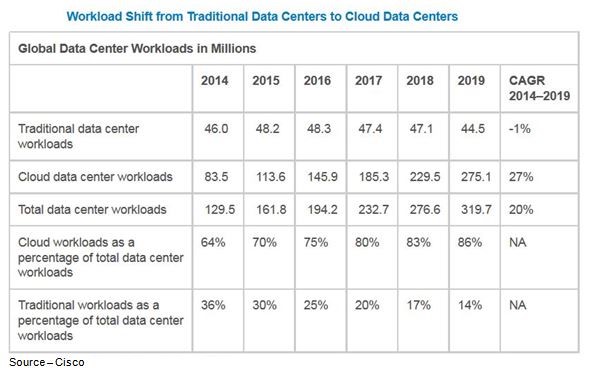
Today, we’ve entered the post-connectivity world. Everyone (especially those under 25) expects everything to be connected whether they’re at the office, home, and school or on the road.
By 2019, 55 percent (2B+ users) of the consumer Internet population will use personal cloud storage, up from 42 percent (1.1B) in 2014.
A growing number of people are hyperconnected to each other and the mobile Web. The Internet becomes their external brain, enabling them to be nimble, quick-acting multitaskers.
Increasingly, firms like Oracle, Salesforce, IBM and Microsoft are developing mobile apps for business applications so people on-the-go can have instant access to company databases and customer files and can proactively assist customers.
Once companies allowed/encouraged employees to BYOD (bring your own device), they found:
– They saved some money not having to buy all those devices
– Folks had a hard time separating work from home so they were “available” more
– People didn’t keep their OSes/apps current or their security
– They mixed the darndest personal/business stuff on their devices
– And clicked on the damnedest, dumbest things
Now that the floodgate has opened; IT managers, carriers and infrastructure owners are trying to figure out how to develop more efficiency in the infrastructures so companies can safely focus on more value-added initiatives such productivity and security.
That’s not easy when most of the “information” in our digital universe is entertainment and social media.
Big Storage – People today increasingly get their news, information and content from the cloud. They spend hours on social media and use their devices-on-the-go to entertain themselves … constantly. And if it’s something they want to keep, they take it to the cloud because it’s there and it’s cheap. Unfortunately, it’s not safe.
You don’t know about it – heck, don’t even think twice about it – but suddenly your company also has to worry about “little” things like copyright, privacy and compliance.
Stuff may not be stored in the company’s servers; but just whip through the corporate network and guess who they’ll sue first?
Yep!
Globally, consumer cloud storage traffic per user will be 1.6GB per month by 2019, compared to 992MB per month in 2014.
Then there’s the little problem that you have all that rich, luscious company data on your devices.
IDC estimates that about one-third of all data requires some type of protection for privacy, regulations or plain old snooping/theft. Right now, only about 20 percent of that data is protected and probably a whole lot less than that when it’s sitting on your devices.
Security? Yeah right!
That’s a concern because people are using their mobile devices for Web searches, banking, reservations, videos/TV/movies, buying tickets, credit transactions, starting their car and about everything else.
According to eMarketer, people spend an average of three hours and 18 minutes on their mobile device; and most of that time is on apps.
In addition, a quarter of the people in developed countries won’t make a single phone call in any given week but they’ll still check their phones 46 times a day.
Cisco estimates that by 2017, global smartphone traffic (201 EB per year) will exceed the amount of data stored (179 EB per year) on those devices – which means more storage in the cloud
The Dark Cloud
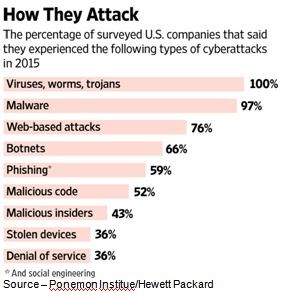
The biggest challenge for firms (and you) is preventing cybercrime – hackers, corporate/nation activity, pros.
One executive noted that, “Working and storing in the cloud is the new wild west. You can expect protection and justice but you quickly find it’s all up to you.”
The concern is rising because spotting it and stopping it is generally reactive – after the fact.
To address the issue, governmental researchers are working on an Enhanced Attribution Program that will characterize the attacker, share his/her modus oprandi with businesses and predict when he/she will strike next.
It sounds almost too good to be true since last year, cyber attacks cost U.S. businesses in every segment (financial, utilities, retail, healthcare, communications, services, education, industrial, hospitality) more than $200 million.
The Dangers – While IT departments struggle to keep company private and intellectual property safe from theft, employees always seem to seek the easy, fast way to do their work and entertain themselves. This leaves less secure, unsecure areas open for hackers and cyberthieves to use to gather personal and corporate information as well as completely disrupt the firm’s business. The challenge is real and growing as folks discover hacking and cybertheft is almost risk free.
Attackers use sophisticated – and not so sophisticated – tools and means to access a firm’s data in the cloud.
Identifying and capturing the perpetrators is difficult for companies and law enforcement. Even when they are caught, it’s a mere slap on the wrist … no big deal!
Management, cybersecurity folks, you and I have to assume our data, IP (intellectual property) has been or will be compromised.
We could stay out of the cloud but in today’s world, that’s impossible!
Protection Moves
Instead of setting up firewalls and feeling smugly safe, companies have to be more proactive in protecting the servers and the apps they and their employees use. Firewalls are okay, but there are always firewall and router exceptions that provide opportunities for bad folks to penetrate.
Firewalls just give you a false sense of security.
Implement strong encryption for everyone, everything, every device. Government agencies might come with paperwork forcing decryption, but at least you know they’re there.
Everyone in the organization – and in your home – has to implement really good passwords for everything they use, everywhere they go. Then, install and use reputable malware and security software on every device/system/thing. Finally, turn on the automated update service for OSes, apps (people forget or put it off) to ensure all the holes are patched.
Educate and train folks to understand that if they have any question/doubt about going to a website, opening an email … don’t!
If they’re wrong about it … it’s okay.
There’s more, but why bother; folks won’t do it anyway.
Remember what Andy Grove (legendary former Intel CEO) said, “Only the paranoid survive.”
Even then Earl Devereaux will say, “I’m glad you’re still wearing that diaper!”
Find a Home-Based Business to Start-Up >>> Hundreds of Business Listings.